Follow Fulldumps.com for future MD-100 updates.
2022 leads4pass MD-100 dumps update with PDF and VCE: https://www.leads4pass.com/md-100.html (314 Q&A)
Newly shared Microsoft MD-100 exam learning preparation program! Get the latest MD-100 exam exercise questions and exam dumps pdf for free! 100% pass the exam to select
the full Microsoft MD-100 dumps the link to get VCE or PDF. All exam questions are updated!
Exam MD-100: Windows 10 – website: https://docs.microsoft.com/en-us/learn/certifications/exams/md-100
leads4pass offers the latest Microsoft MD-100 PDF Google Drive
[Latest updates] Free Microsoft MD-100 dumps pdf download from Google Drive: https://drive.google.com/file/d/13PjH9pbNL0EpbtJDlUdAQ_YBQliaIQ5_/
Examineeverything Exam Table of Contents:
- Microsoft MD-100 Practice testing questions from Youtube
- latest updated Microsoft MD-100 exam questions and answers
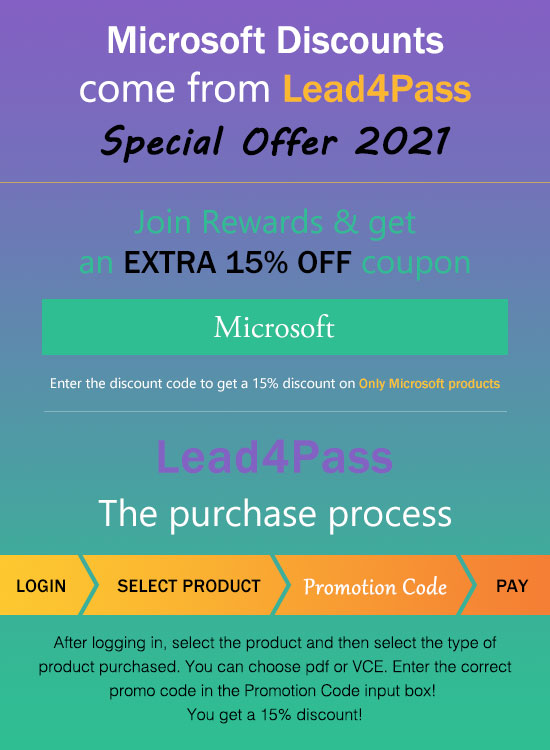
- leads4pass Microsoft Discount code 2021
- About leads4pass
Microsoft MD-100 Practice testing questions from Youtube
latest updated Microsoft MD-100 exam questions and answers
QUESTION 1
You need to meet the technical requirements for the San Diego office computers. Which Windows 10 deployment method should you use?
A. wipe and load refresh
B. in-place upgrade
C. provisioning packages
D. Windows Autopilot
Correct Answer: D
References: https://docs.microsoft.com/en-us/windows/deployment/windows-autopilot/windows-autopilot
QUESTION 2
You have a computer named Computer1 that runs Windows 10. Computer1 is in a workgroup. Computer1 contains the
folders are shown in the following table.![[2021.1] leads4pass md-100 exam questions q2](https://www.examineeverything.org/wp-content/uploads/2021/01/q2.jpg)
User1 encrypts a file named File1.txt that is in a folder named C:\Folder1.
What is the effect of the configuration? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:
![[2021.1] leads4pass md-100 exam questions q2-1](https://www.examineeverything.org/wp-content/uploads/2021/01/q2-1.jpg)
QUESTION 3
You have a computer named Computer1 that runs Windows 10.
From Event Viewer on Computer1, you have a task named Action1 that is attached to the following event:
Log: System Source: Kernel-General Event ID: 16
You need to modify the settings of Action1. What should you use?
A. the Settings app
B. Task Scheduler
C. Event Viewer
D. System Configuration
Correct Answer: C
An Event Viewer task is created and modified in the Event Viewer.
References: https://www.techrepublic.com/article/how-to-use-custom-views-in-windows-10s-event-viewer/
QUESTION 4
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains
a unique solution that might meet the stated goals. Some question sets might have more than one correct solution,
while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not
appear on the review screen.
You have a computer named Computer1 that runs Windows 10.
You test Windows updates on Computer1 before you make the updates available to other users at your company.
You install a quality update that conflicts with a customer device driver.
You need to remove the update from Computer1.
Solution: From System Restore, you revert the system state to a restore point that was created before the update was
installed.
Does this meet the goal?
A. Yes
B. No
Correct Answer: B
References: https://support.microsoft.com/en-us/help/934307/description-of-the-windows-update-standalone-installer-inwindows
QUESTION 5
HOTSPOT
You have two computers named Computer1 and Computer2 that run Windows 10. The computers are in a workgroup.
You perform the following configurations on Computer1:
1.
Create a user named User1.
2.
Add User1 to the Remote Desktop Users group.
You perform the following configurations on Computer2:
1.
Create a user named User1 and specify the same user password as the one set on Computer1.
2.
Create a share named Share2 and grant User1 Full control access to Share2.
3.
Enable Remote Desktop.
What are the effects of the configurations? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:![[2021.1] leads4pass md-100 exam questions q5](https://www.examineeverything.org/wp-content/uploads/2021/01/q5.jpg)
QUESTION 6
Your network contains an Active Directory domain named contoso.com. The domain contains named Computer1 that
runs Windows 10.
On Computer1, you create an NTFS folder and assign Full Control permissions to Everyone.
You share the folder as Share1 and assign the permissions shown in the following table.![[2021.1] leads4pass md-100 exam questions q6](https://www.examineeverything.org/wp-content/uploads/2021/01/q6.jpg)
When accessing Share1, which two actions can be performed by User1 but not by User2? Each correct answer
presents part of the solution. NOTE: Each correct selection is worth one point.
A. Delete a file created by another user.
B. Set the permissions for a file.
C. Rename a file created by another user.
D. Take ownership of the file.
E. Copy a file created by another user to a subfolder.
Correct Answer: BD
References: https://www.varonis.com/blog/ntfs-permissions-vs-share/
QUESTION 7
HOTSPOT
Your network contains an Active Directory domain named contoso.com. The domain contains two computers named
Computer1 and Computer2 run Windows 10 and are joined to the domain.
On Computer1, you create an event subscription named Subscription1 for Computer2 as shown in the Subscription1
exhibit. (Click the Subcription1 tab.)![[2021.1] leads4pass md-100 exam questions q7](https://www.examineeverything.org/wp-content/uploads/2021/01/q7.jpg)
Subscription1 is configured to use forwarded events as the destination log.
On Computer1, you create a custom view named View1 as shown in the View1 exhibit. (Click the View1 tab.)
![[2021.1] leads4pass md-100 exam questions q7-1](https://www.examineeverything.org/wp-content/uploads/2021/01/q7-1.jpg)
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
Hot Area:
![[2021.1] leads4pass md-100 exam questions q7-2](https://www.examineeverything.org/wp-content/uploads/2021/01/q7-2.jpg)
QUESTION 8
Your network contains an Active Directory domain. The domain contains 10 computers that run Windows 10. Users in
the finance department use computers.
You have a computer named Computer1 that runs Windows 10.
From Computer1, you plan to run a script that executes Windows PowerShell commands on the finance department
computers.
You need to ensure that you can run the PowerShell commands on the finance department from Computer1.
What should you do with the finance department computers?
A. From the local Group Policy, enable the Allow Remote Shell Access setting.
B. From the local Group Policy, enable the Turn on Script Execution setting.
C. From the Windows PowerShell, run the Enable-MMAgent cmdlet.
D. From the Windows PowerShell, run the Enable-PSRemoting cmdlet.
Correct Answer: D
References: https://docs.microsoft.com/en-us/powershell/module/microsoft.powershell.core/enablepsremoting?view=powershell-6
QUESTION 9
You need to meet the quality update requirement for the computer. For how long should you defer the updates?
A. 14 days
B. 10 years
C. 5 years
D. 180 days
E. 30 days
Correct Answer: B
References: https://docs.microsoft.com/en-us/windows/deployment/update/waas-overview
QUESTION 10
Your network contains an Active Directory domain named contoso.com. The domain contains the users shown in the
following table.![[2021.1] leads4pass md-100 exam questions q10](https://www.examineeverything.org/wp-content/uploads/2021/01/q10.jpg)
You have a computer named Computer1 that runs Windows 10 and is in a workgroup.
A local standard user on Computer1 named User1 joins the computer to the domain and uses the credentials of User2
when prompted.
You need to ensure that you can rename Computer1 as Computer33.
Solution: You use the credentials of User4 on Computer1.
Does this meet the goal?
A. Yes
B. No
Correct Answer: B
Renaming a domain-joined computer will also rename the computer account in the domain. To do this, you need
domain administrator privileges.
User4 is a server operator, not an administrator. Members of the Server Operators group can sign in to a server
interactively, create and delete network shared resources, start and stop services, back up and restore files, format the
hard disk
drive of the computer, and shut down the computer.
Use User3\\’s credentials instead.
References:
https://docs.microsoft.com/en-us/windows/security/identity-protection/access-control/active-directory-securitygroups#bkmk-domainadmins
QUESTION 11
HOTSPOT
You need to reduce the amount of time it takes to restart Application1 when the application crashes.
What should you include in the solution? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
Hot Area:![[2021.1] leads4pass md-100 exam questions q11](https://www.examineeverything.org/wp-content/uploads/2021/01/q11.jpg)
Correct Answer:
![[2021.1] leads4pass md-100 exam questions q11-1](https://www.examineeverything.org/wp-content/uploads/2021/01/q11-1.jpg)
Reference: https://www.howto-connect.com/how-to-attach-a-task-to-this-event-in-event-viewer-in-windows-10/
QUESTION 12
Note: This question is part of a series of questions that present the same scenario. Each question in the series contains
a unique solution that might meet the stated goals. Some question sets might have more than one correct solution,
while
others might not have a correct solution.
After you answer a question in this section, you will NOT be able to return to it. As a result, these questions will not
appear on the review screen.
A user named User1 has a computer named Computer1 that runs Windows 10. Computer1 is joined to an Azure Active
Directory (Azure AD) tenant named contoso.com. User1 joins Computer1 to contoso.com by using
[email protected].
Computer1 contains a folder named Folder1. Folder1 is in drive C and is shared as Share1. Share1 has the permission
shown in the following table.![[2021.1] leads4pass md-100 exam questions q12](https://www.examineeverything.org/wp-content/uploads/2021/01/q12.jpg)
A user named User2 has a computer named Computer2 that runs Windows 10. User2 joins Computer2 to contoso.com
by using [email protected].
User2 attempts to access Share1 and receives the following error message: “The username or password is incorrect.”
You need to ensure that User2 can connect to Share1.
Solution: In Azure AD, you create a group named Group1 that contains User1 and User2. You grant Group1 Modify
access to Folder1.
Does this meet the goal?
A. Yes
B. No
Correct Answer: A
References: https://docs.microsoft.com/en-us/previous-versions/windows/it-pro/windowsserver-2008-R2-and-2008/cc754178(v%3dws.10)
QUESTION 13
You have a computer named Computer1 that runs Windows 10.
On Computer1, you create the local users shown in the following table.![[2021.1] leads4pass md-100 exam questions q13](https://www.examineeverything.org/wp-content/uploads/2021/01/q13.jpg)
Which three user profiles will persist after each user signs out? Each correct answer presents part of the solution.
NOTE: Each correct selection is worth one point.
A. User1
B. User2
C. User3
D. User4
E. User5
Correct Answer: ADE
leads4pass Microsoft Discount code 2021
leads4pass shares the latest Microsoft exam Discount code “Microsoft“. Enter the Discount code to get a 15% Discount!
About leads4pass
leads4pass has 8 years of exam experience! A number of professional Microsoft exam experts! Update exam questions throughout the year! The most complete exam questions and answers! The safest buying experience! The greatest free sharing of exam practice questions and answers!
Our goal is to help more people pass the Microsoft exam! Exams are a part of life, but they are important!
In the study, you need to sum up the study! Trust leads4pass to help you pass the exam 100%!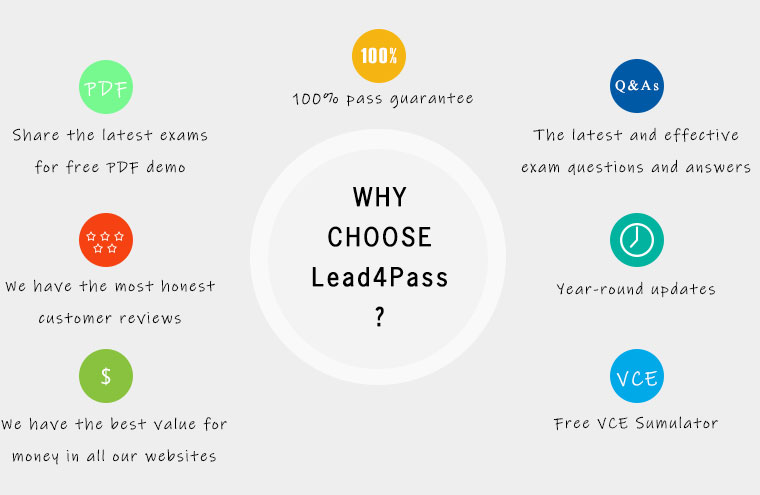
Summarize:
Examineeverything free to share Microsoft MD-100 exam exercise questions, MD-100 pdf, MD-100 exam video! leads4pass updated exam questions and answers throughout the year!
Make sure you pass the exam successfully. Select lead4Pass MD-100 to pass Microsoft MD-100 exam “Windows 10“.
ps.
Latest update leads4pass MD-100 exam dumps: https://www.leads4pass.com/md-100.html (211 Q&As)
[Latest updates] Free Microsoft MD-100 Dumps pdf download from Google Drive: https://drive.google.com/file/d/13PjH9pbNL0EpbtJDlUdAQ_YBQliaIQ5_/